
In today’s cyber-sensitive world, data protection is necessary. Developers and IT experts need to place “4D security” high on their radar as businesses rely more than ever on connected applications. When you build internal systems or customer-facing apps, securing your 4D server helps keep data accurate, confidential, and accessible.
If you have already asked how to secure your 4D server, you are not alone. This article will look at the fundamentals of security. Authentication, 4D SSL encryption and access control. It will also provide insights into Wizmo, a popular provider of 4D hosting, consulting and managed services.
Table of Contents
Why 4D Security Matters
Worldwide, enterprises use 4D applications to drive performance. Even though 4D is a strong framework, we still need to configure it properly to ensure it protects us from modern-day attacks like getting our credentials stolen, having our data intercepted, or having the database accessed in an unauthorised manner.
- Implementing a secure 4D server helps you.
- Protect sensitive data through encryption.
- Implement robust identity checks with 4D user authentication.
- Prevent unauthorized database queries.
- Maintain compliance with data privacy regulations.
Your 4D server will operate fine even in a complex IT setup, courtesy of the combination of technical configuration and procedural discipline that’s used.
How to Secure a 4D Server
Many developers question “How to secure a 4D server?”, which is much more than just enabling SSL. To secure your 4D server, you must have a combination of security features in place.
Step 1: Install strong 4D user authentication
- The foundation of 4D security is authentication. Every user must be authenticated before entering your environment
- 4D User Authentication Best Practices.
- Require passwords to contain characters of varying types.
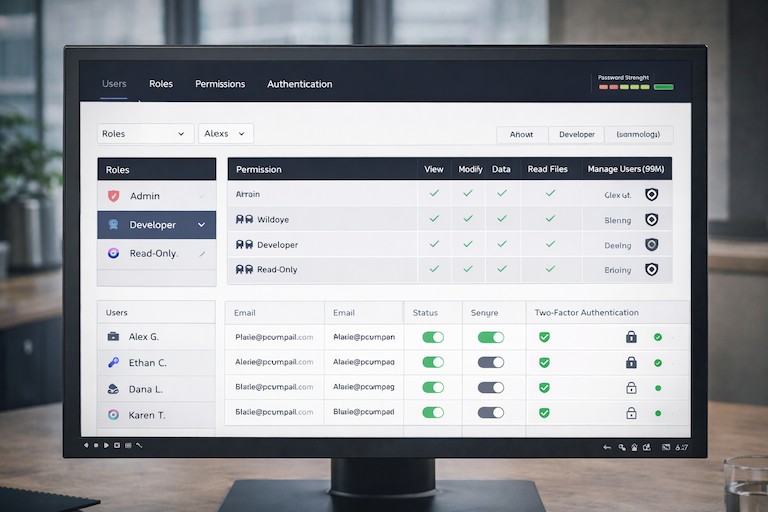
- Permission Sets let you assign roles (admin, developer, read-only) to control access at a granular level.
- Employ Two-Factor Authentication (2FA) as an extra layer of verification
- Separate reviews of accounts to quickly disable inactive users.
- To mitigate the risk of credential compromise, enforce permission sets and strong password policies.
At Wizmo, we assist organizations in deploying enterprise-grade 4D user authentication systems built on global standards like ISO 27001 and SOC 2.
Step 2: Enable 4D SSL Encryption (TLS)
Encryption is the backbone of 4D security. With advanced TLS protocols for 4D SSL encryption, all client-server communication is protected as per ITU recommendations.
Can I enable SSL in 4D?
Yes! 4D has built-in options to enable SSL on HTTP and database connections.
Best Practices for 4D SSL Encryption
Always use valid TLS certificates (don’t use self-signed in production).
- Enforce HTTPS for all traffic.
- Regularly renew certificates.
- Utilise the latest versions of TLS (1.2 or 1.3).
- Strong 4D security encrypts messages using SSL configured well to allow no eavesdropping, tampering, or man-in-the-middle attacks.
Step 3: Implement Detailed Access Control
Once you are authenticated and encryption is in place, access control determines who can do what.
- Access Control Strategies.
- Access is defined by role and not individual.
- Controls at Object Level: Limit access to specific tables or methods
- Separate production and test databases.
- Keep track of everything through logging.
- Powerful access control does more than just shield sensitive data; it creates room for development on a 4D server.
Step 4: Regularly Schedule a 4D Security Audit
Security isn’t static—it evolves. A regular 4D security audit at least 2 times a year helps mitigate risks.
A complete 4D security audit typically includes
- Authentication and permission review.
- TLS certificate checks.
- Software and plugin updates.
- Log file and anomaly analysis.
Wizmo’s 4D security consultants provide in-depth audits by employing automation and expert manual testing to help discover vulnerabilities before attackers do.
Advanced 4D Security Techniques
- For vital systems, implement advanced protection strategies for 4D security beyond the basics.
- Data-Level Encryption means to encrypt database sensitive fields.
- Network firewalls limit outer connections to internal ones.
- A system to detect network abuse
- Backups Encrypted with AES-256 Encryption
These techniques help harden your secure 4D server environment for reliability and compliance.
Common 4D Security Mistakes to Avoid
Even experienced teams can make small missteps that weaken an otherwise solid 4D security posture. Common issues include:
Default or weak administrator credentials
Expired or misconfigured TLS certificates
Failing to review or act on security logs
Over-permissioned user or service accounts
Disabling SSL for testing and never re-enabling it
A strong 4D security stack relies on consistent enforcement across every layer. One overlooked configuration can become the weakest link—and ultimately define your exposure.
Staying Ahead of Evolving 4D Security Threats
Cyber threats are not static. They change constantly, and security practices must evolve alongside them. The 4D ecosystem continues to advance with updated TLS standards, stronger encryption protocols, and more sophisticated access management tools.
The challenge for many organizations isn’t awareness—it’s execution. Teams often lack the time or specialized expertise required to continuously implement, validate, and maintain these protections across production environments.
This is where a long-term 4D security strategy becomes essential.
Why a Proactive 4D Security Strategy Matters

Investing in security before an incident occurs is significantly less costly than responding after the fact. Security failures can impact far more than just a server—they can disrupt uptime, damage business reputation, and erode customer trust.
A proactive 4D security approach focuses on prevention, scalability, and compliance from the start. Rather than applying generic fixes, it accounts for how your systems operate, how users connect, and how data must remain protected as your environment grows.
Partnering With Wizmo for Expert 4D Security Guidance
No two 4D environments are alike. Securing one properly requires deep platform knowledge and an understanding of how 4D operates behind the scenes.
Wizmo works directly with organizations to strengthen their 4D environments through:
Security audits and risk assessments
SSL/TLS encryption configuration and maintenance
Authentication and access control design
Ongoing monitoring and security hardening
When you work with Wizmo, you’re not purchasing a one-time technical service. You’re gaining a partner focused on protecting your entire 4D ecosystem. Our team proactively identifies vulnerabilities, refines access policies, and keeps encryption aligned with current security standards.
Ready to Strengthen Your 4D Security?
Securing a 4D server is an ongoing effort that requires consistent authentication, encryption, and access control working together over time.
Wizmo’s 4D security consulting helps organizations identify risks, strengthen configurations, and maintain secure environments through audits, monitoring, and ongoing security hardening.
Connect with Wizmo to review your 4D security approach and discuss next steps.

